Events

This unique hands-on course combining BLE and NFC security trainings aims to provide solid understanding of security aspects for both technologies, along with practical skills and included hardware tools for hands-on exercises.
Several editions are scheduled for 2022 - both traditional (in-person) and online, suitable for various time zones around the world.

Bluetooth Low Energy is one of the most exploding IoT technologies. BLE devices surround us more and more – not only as wearables, toothbrushes and sex toys, but also smart locks, medical devices and banking tokens. Alarming vulnerabilities of these devices have been exposed multiple times recently. And yet, the knowledge on how to comprehesively assess their security seems very uncommon. This is probably the most exhaustive and up to date training regarding BLE security – for both pentesters and developers.
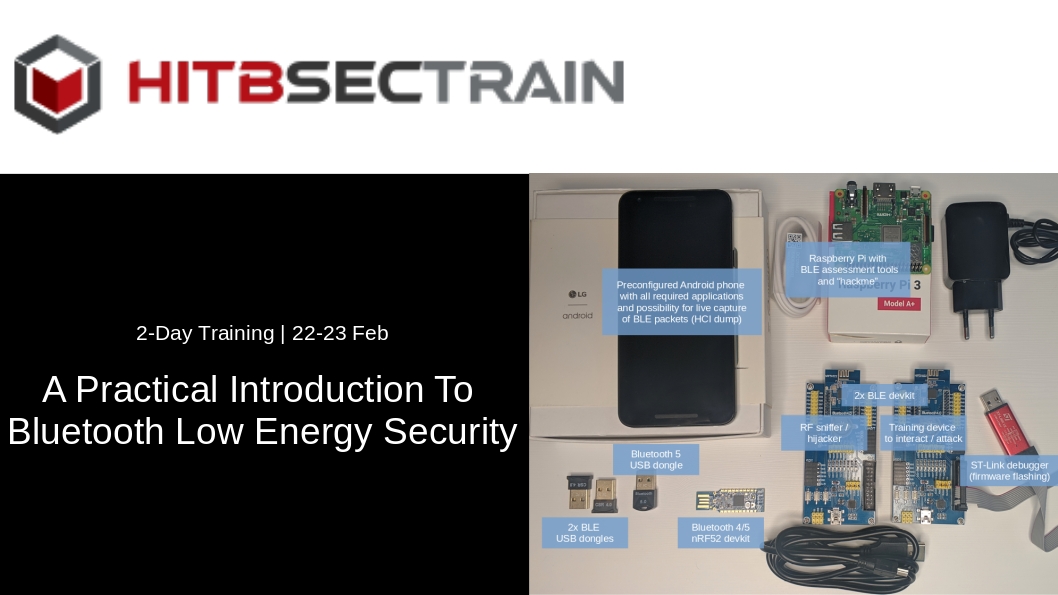
The training has been prepared for remote hands-on participation. Each attendee will receive a hardware pack of 200 USD value, shipped in advance (please register as soon as possible!). The hardware includes among others a preconfigured Android smartphone, BLE sniffer, BLE dedicated training device and Raspberry Pi (details below). With the specially arranged setup, participants will be able to perform hands-on practical exercises not only during virtual session but also any time later.