Bluetooth Low Energy HackMe: the best way to learn BLE security basics while having fun!
Bluetooth Low Energy HackMe is is a free, open source tool: hands-on practical introduction to BLE security - without the need of any special hardware. Application simulates various BLE devices using your laptop's built-in Bluetooth adapter. You can actively learn by solving practical hacking challenges using nothing more than just a phone.

Bluetooth Low Energy hardware-less HackMe is a free tool that aims to help getting familiar with the very basics of ubiquitous BLE technology and its (in)security - without the need of any dedicated hardware, nor sophisticated prior knowledge. It is based on a specially designed software (running on a typical Windows 10 laptop) - which simulates various BLE devices, on the radio layer working exactly the same as real ones. Hands-on challenges of increasing level - starting with simple introduction up to unlocking smart locks - allow for practical experience, the best possible way to learn.
All of these challenges can be solved using nothing more than just a free Android mobile application, which connects via Bluetooth to the laptop running simulated devices. This unique approach makes the fun available for everyone who would like to start the journey into fascinating vulnerabilities of BLE devices, but afraid of gearing up with special hardware or steep learning curve for advanced tools. In a series of tasks to solve you will get familiar with BLE advertisements, beacons, connections, take control over BLE smart bulb, reverse-engineer the communication protocol, brute force passwords, and hack real smart lock. The techniques learned by solving these tasks can later be easily applied to take control of surprisingly lots of real devices surrounding us, and are a solid foundation for further mastering the topic.
Requirements
Windows computer
The HackMe is designed to run on a typical Windows 10 laptop (version at least 1803) with built-in Bluetooth 4 (or 5) interface and should work on majority of recent, less than 5 years old laptops. For one of the tasks, installing a free Wireshark network analyser and downloading previously sniffed dump file will be needed (detailed instruction provided in the relevant section of HackMe).
In a rare case when your Windows system is “N” version (for example Windows 10 Home N, Windows 10 Pro N, Windows 10 Education N, Windows 10 Enterprise N), you will have to install additional, free “Media Feature Pack for N versions of Windows 10”. Otherwise some tasks which involve Text To Speech functionality (for example talking smart light bulb) will not work for you. If your system already has Windows Media Player available, you are good to go.
It may not work with external USB Bluetooth dongle, at least the most popular, CSR8510-based has been confirmed incompatible, despite supporting Bluetooth 4. The restrictions come from internal Windows BLE API, and until Microsoft updates it, there is nothing much we can do about it. Fortunately, the HackMe has been confirmed working with Realtek 8761B-based BLE USB. These are often sold as “BLE 5 USB dongle”, but be aware that some of the offers may be fake. Checking driver details before buying may help.
If you would like to run the HackMe in Windows running inside virtual machine, your options are:
- getting compatible USB dongle (currently Realtek 8761B-based ones are confirmed working) and connecting it via USB to VM,
- having laptop with internal Bluetooth adapter connected to USB bus not PCI (confirmed working for example for Lenovo Thinkpad X1 Carbon 7) - possible to setup direct USB pass-through to VM.
Android phone
The tasks were designed to be solved using free Android application nRF Connect for Mobile, chosen for its unique, useful features (low level debug information, macro scripts, …). Hence Android phone with Bluetooth 4 (at least Android 5.0, so basically any non-severly obsolete model) is recommended.
There is also iOS version of this application, but with severly limited functionality - as iOS limits low-level access to Bluetooth for applications. As a result, you will not be able to solve most of the tasks using iPhone (however still a few will be possible).
Another possibility is to use other BLE tools, running for example on Linux or Mac system. Details however are not covered in the HackMe instructions.
Background knowledge
Technical background will be helpful for solving the tasks, but is not essential. No prior knowledge of Bluetooth is required.
Download and install
The software is available in Microsoft store:
https://www.microsoft.com/store/apps/9N7PNVS9J1B7
Source code is published on GitHub: https://github.com/smartlockpicking/BLE_HackMe, and can be compiled/edited/debugged using free Microsoft Visual Studio Community edition.
It is licensed on MIT permissive free software license, which allows to use and modify it without restrictions. Of course you are encouraged to share your code updates with community.
Running HackMe
Initial compatibility check
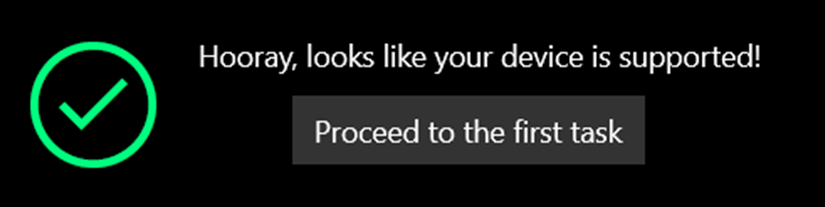
Right after starting, the application will check if the system’s Bluetooth interface is supported.
The successful check will end up with following message:
 In case your Bluetooth adapter is not supported (or turned off), you will see an error:
In case your Bluetooth adapter is not supported (or turned off), you will see an error:
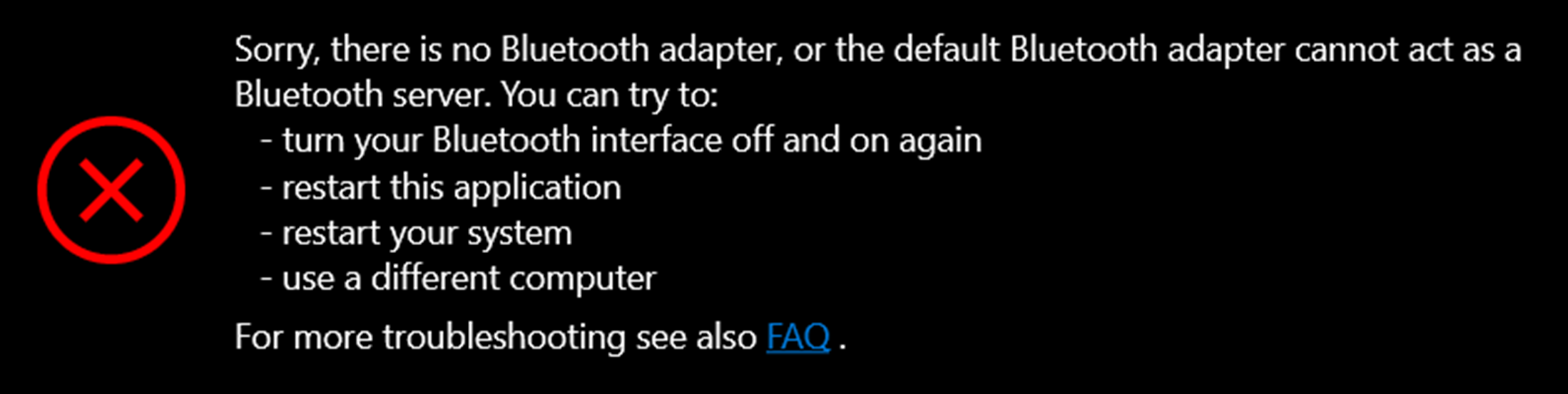 Try following the suggestions, but in case it does not help, your system is unfortunately unsupported.
Try following the suggestions, but in case it does not help, your system is unfortunately unsupported.
Solving tasks
In the left navigation pane is a list of tasks to be solved. They are designed to be followed in sequence (skills learned in previous ones are used to solve the next), but you are free to “jump” out of order.
Each challenge page starts with a short theory introduction, followed by the task description. Depending on task, in order to solve it you may need to submit some response (for example previously read from simulated device via BLE), or somehoow interact with graphical representation of device - like turn on the light bulb or unlock smart lock.
The tasks should be self-explanatory. But in case of having trouble, try hitting the button down in “Hints” section. It is however suggested to leave it as a “last resort” - spoilers may affect the fun. In case all of the available hints still did not help, check Frequently Asked Questions and issues (feel free to file your own).
Progress status
Progress bar on top shows current number of solved tasks. The last navigation section, “Summary”, outlines a detailed list of tasks and their status.
As of today, the application does not save the status of progress, which will be reset to “0” after restarting. It is a feature planned for some next, future release.
Troubleshooting
In case you experience some instability with Bluetooth (for example device not visible any more), turning the Bluetooth adapter on and off, restarting the application or your system may help.
If the problem persists, or you found any bug (like application crash, something does not work like expected), please submit it to Github issues Be sure to check also current FAQ.
Events
The new HackMe has been showcased during several events, including:
- HackInTheBox CyberWeek 2020:
Introduction to Bluetooth Low Energy security lab (18.11.2020).
Slides: A practical introduction to BLE security without any special hardware (PDF, 16M)
Recording:
- BlackHat EU 2020 Arsenal (10.12.2020): Slides: BlackHat EU 2020 Arsenal BLE hardware-less HackMe (PDF, 8M)
Recording:
Share this post
Twitter
Google+
Facebook
Reddit
LinkedIn
StumbleUpon
Email