Hardwear.io 2018
BLE security essentials

Bluetooth Low Energy (Smart, 4) is recently gaining more and more traction as one of the most common and rapidly growing IoT technologies. Unfortunatelly the prevalence of technology does not come with security. Alarming vulnerabilities in BLE smart locks, medical devices and banking tokens are revealed day by day. And yet, the knowledge on how to comprehensively assess them seems very uncommon.
In this workshop you will get familiar with the basics of BLE security. We will work on a dedicated, readily available BLE hardware nRF devkit device. You will learn how to program and flash it yourself, using special web interface and ready templates. Such approach allows to better understand how things work “under the hood”, experiment with different options, and then secure the hardware properly.
From attacker’s perspective, we will cover among others: sniffing, spoofing, MITM, replay and relay.
Having enough time, we will play with a collection of vulnerable smart locks, sex toys and other devices.
Please bring
- contemporary laptop that can run Kali Linux in VM (like 4 GB RAM, 20G disk space), with VM software of your choice installed (virtualbox or vmware), and at least 2 USB ports available
- smartphone with BLE support, preferably Android (at least 4.3), or iPhone (at least 4s)
- if you have Raspberry Pi 3 or BBC micro:bit, you can bring it too
- you can also bring your own BLE devices
The hardware set
The workshop will be performed on a following hardware set:
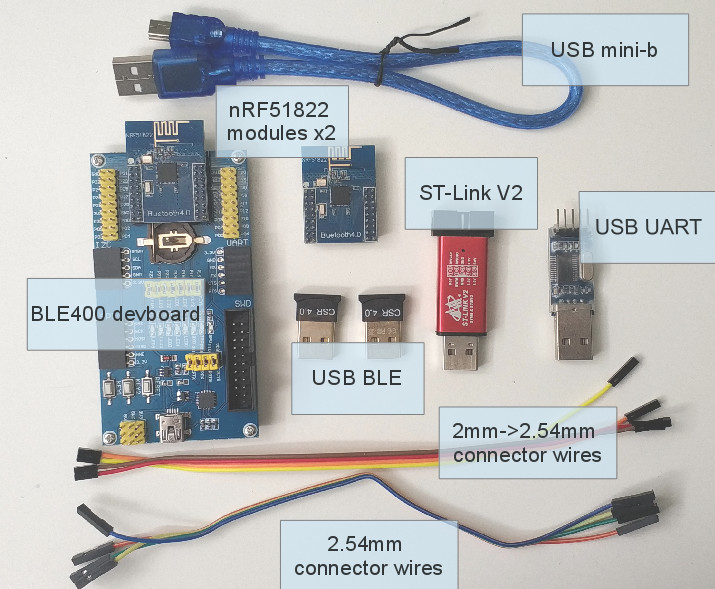
- BLE400 development board + nRF51822 Core module. The module can be flashed as a BLE RF sniffer (Nordic, or BtleJack), as well as an individual device to attack
- ST-Link V2 debugger for flashing the devkit firmware
- BLE USB dongles
- USB UART
- connector wires
You can easily buy the hardware yourself on Aliexpress, Ebay, Amazon and probably in local electronics store. For your convenience we will prepare such sets to buy during workshop - for 30 EUR (without profit).
Registration
Register to the conference here:
https://hardwear.io/register.php
Slides
Download the workshop slides here.
Share this post
Twitter
Google+
Facebook
Reddit
LinkedIn
StumbleUpon
Email